Sales: 678.967.3854
Support: 866.252.6363
What We Do
Who We Serve
Success Stories
Latest Thinking
LATEST THINKING
About Us

About 18 months ago, our DynaSis team put together an extensive system review/planning program for our clients that we call our Strategic Technology Plan, or STP for short. We have always performed, and still do, complementary IT assessments for potential clients, but while these are extremely effective in determining weaknesses in a company’s IT network, the STP goes much deeper in highlighting very specific items that need to be addressed, and ranks them in order of priority: high, medium and low.
Over the next couple of months, we will be releasing a series of articles designed for the layman that are intended to provide a great deal of necessary education about today’s information technology, and we will do it in language the average C-Level business executive can understand.
Those of us involved in providing technology solutions to the business world are very often guilty of seeming to intentionally make everything related to technology very confusing. Some people in the technology world believe that this level of confusion helps their own business interests, assuming that if the prospect can’t understand it, he will feel more pressure to hire someone who does.
We don’t believe this. We do agree that technology today is extremely complex, but we feel that if we explain it in terms everyone can understand, the typical business-person will be more inclined – not less – to take appropriate actions to protect their businesses. We don’t expect the typical layman to intuitively know what a DRAC/iLO card is for, or why they should be using “virtual machines” or what a “RAID configuration” is all about. Similarly, if you had never seen a baseball game, would you understand the terms “slider”, or “squeeze play”, or “balk”, or “fielder’s choice?” So why would you understand technology terms when hearing them for the first time?
The topics we will be covering include:
Our goal is to make our clients and other readers aware of how and why we believe frequent checking and possible upgrading are necessary, and what the potential downsides can be for failing to do so. We are also going to break everything down into language that is understandable to most. One caveat: there can be many, many variations within each category and sub-category we are going to discuss, so to keep the information manageable, there will be times that we give you only the basics.
First, let’s understand what a server is. Many people think of a server as a large computer, but don’t really understand what it accomplishes. A “server” in fact, is not a computer, but rather a program that resides in a computer, and, yes, the computer hosting the server program is generally larger and more reliable than the typical desktop or laptop computer. A single computer of the right size can host multiple server programs. The server “serves” multiple “clients”, a client being the actual desktop or laptop computer. The server serves its clients by providing functionality, such as sharing data and performing calculations. The advantage is that all the files that would be used by the client are more safely stored in the server computer, plus the sharing of data, including the results of calculations, means that many people can benefit from colleagues’ work.
Here are the things we check on relative to servers during the STP:
Are the servers properly spec’d for the applications they host? We observe the utilization of the servers’ resources as it affects the applications and estimate anything that may need to be resized. Key factors are the processor, RAM and disc utilization. We do this because if the servers do not have sufficient resources for the applications, or for the number of users, it can adversely affect performance.
Is the warranty current and is the SLA acceptable? The SLA – Service Level Agreement – states the obligations of the manufacturer for replacement or repair in terms of guaranteed time for repair or placements, and for parts that may be necessary. We consider next business day the minimum acceptable for critical parts. We consider this to be of high priority.
Do all servers have redundant power supplies and are they plugged in? (We do find unplugged devices. Don’t confuse this with the UPS, or uninterruptable power supply – next topic.) The redundant power supply is internal, in other words, two power packs within the unit in case one fails.
UPS – Uninterruptable Power Supply. This is the box into which the computer is plugged and that then gets plugged into the wall. This is the device that provides temporary power when electrical power to the building goes out. Also to be noted is that the batteries in these units have a defined life span and need to be replaced periodically. This is a high priority item.
DRAC/iLO card installation and configuration. This may be a term with which you are unfamiliar, but this card provides your IT service the ability to log in and reboot a frozen server, which can result in faster problem resolution, the avoiding of dispatching a technician, and significantly reduced downtime.
Are the partitions set up in proper sizes for the operating system? This is important for maximum operating efficiency.
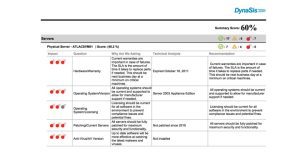 Is the version of the operating system that is installed on the server current? It is not necessary that the OS be the most current, but it is important that the version is still supported by the manufacturer in case support is required. We consider this high priority.
Is the version of the operating system that is installed on the server current? It is not necessary that the OS be the most current, but it is important that the version is still supported by the manufacturer in case support is required. We consider this high priority.
Are operating system licenses current? Microsoft does perform audits and can charge penalties for non-compliance, as do a number of other companies. Additionally, as a business executive yourself, you are aware that companies that develop the software upon which you depend have invested a great deal on time, effort and capital in the development of this software and are entitled to continuing revenue from its use.
Does each administrator have his/her personal login? We sometimes find that administrators share a default admin account. When this happens, it often becomes impossible to determine who is responsible for certain changes or for permissions that have been granted. As a security matter, we consider this to be high priority.
Is the company using security screen locks? The screens on all computers should lock if the device has not been used for a certain period of time so as to prevent unauthorized use. Computers left unprotected can be used after hours, before work, or during breaks when no one is around.
Is proper up-to-date web security in place? This includes Internet Explorer Enhanced Security, OpenDNS, as well as a company policy to not permit browsing from servers. Servers should never be used to access the Internet except for specific purposes such as software updates.
Are the company’s servers managed and monitored for patching? Servers that are managed have been shown to have better uptime and be less likely to be infected with malware.
Have the servers been patched with the latest patches? Patches fix vulnerabilities that enable cyber criminals access to your computers. The patches also solve problems with the software’s functionality, or add new functionalities. We are sometimes asked why software is released before it is “perfect”. Simply put, modern software is incredibly complex. It is estimated that Microsoft Office is made up of 40+ million lines of code. Although most software is tested and retested before release, it is impossible to test every possible situation that may arise when 100s of millions of people end up using it, along with thousands of very smart cyber criminals. This is a high priority item.
Is patching managed centrally? This allows for much more consistent and rapid updating, and, thereby, not letting the systems fall behind.
Are all anti-virus software and definitions up-to-date? It is critical that the latest versions of anti-virus software be installed as the newest versions contain the latest and best defenses against all types of malware, including ransomware that has become so widespread.
In it, we will cover virtualization, plus we will take a look at Data Structure and Storage, again, in layman’s terms. We will also discuss how we examine individual desktop and laptop computers to make sure they are secure, providing top performance, and lasting as long as possible.
The intention of this series to educate you so you can fully participate in important technology decisions for your company. If there are specific topics you would like covered, or if you have any questions on topics covered in this piece, please contact us at Info@DynaSis.com.
