Sales: 678.967.3854
Support: 866.252.6363
What We Do
Who We Serve
Success Stories
Latest Thinking
LATEST THINKING
About Us
Netflix, UPS, Facebook, your bank, and your power company are all companies that you receive emails from regularly. These are the companies that cyber attackers will use to send their phishing emails from to capture your personal information or to install malware on your device. These brands are sophisticated and believable. People click on these emails without thinking twice. Our job at DynaSis, a managed IT service company in Atlanta, is to educate our users on signs to look for that indicate the email is a phishing scam.
There are some proactive things you can look for to protect yourself from these attacks, and by working with DynaSis for IT support, we have the systems and tools available to help keep these emails out of your inbox.
So, what do you do if you find yourself as part of a successful phishing email scam? Here are a few self-recovery steps to take to after clicking on a phishing email.
The best way to avoid a phishing attack is to be aware of what to look for. Learn more about How to Prevent Scams, Phishing and Mis-Sent Emails. DynaSis, a managed IT services company in Atlanta, has the products and tools to help keep you and your staff educated on cyber threats and how to be prepared. Fill out our form today or call 770.629.9615 to learn more about how DynaSis can help keep your company safe.
DynaSis: The Right Choice for Your IT Support
Last week we began our discussion on disaster recovery with a look at RPO (Recovery Point Objective), RTO (Recovery Time Objective), and MTO (Maximum Time Objective). This week we’re going to give you a little insight in how IT companies set these parameters. Of course, there is no magic bullet or yellow brick road to instantaneously give us answers, but if you start with some good information, you are probably going to get good solutions. A large part of your calculation will consider how much the cost will be if your business is effectively shut down for any length of time.
How much do most businesses lose because of IT problems? A study by Coleman Parks Research not too long ago estimated that small businesses lose an average of $55,000 a year due to downtime, data loss, and the cost of recovery. Mid-sized businesses are losing an average of $91,000. And these losses are before any major disaster. You may be asking, why aren’t I seeing this loss? How can it actually exist if I am not seeing it? IT companies know the answer is that it occurs in almost unnoticeable dribs and drabs. It’s the customer complaint that isn’t answered properly because accurate records couldn’t be found. Or business lost because the phone system was down for ten minutes. Or, even worse, angry customers because of a data breach. Yes, small companies suffer data breaches. You don’t hear about them because the media isn’t interested in the losses of a small company.
Your first step in understanding your potential loss should be the creation of a Business Impact Analysis. Many IT companies will have a version of this to help you implement. The primary steps include:
1: Create a list of your business’s core functions and the data required to keep these functions running. This includes processes critical to generating revenue: sales, accounting, etc. You should be including customer/client contacts, purchase orders and contract items, accounting and your other corporate records, as well as any other documents that will prove important to your business continuity.
2: Supporting infrastructure: what will you need if you have to replace damaged or destroyed equipment and/or software in the event of fire, flood, storm, or theft? It’s important to know what you will need to get your business up and running again. AND you need to know where and how you will obtain everything. Every day you are not operating, you are losing money.
3: Calculate your potential losses. Work with your accountant or in-house financial officer to figure out how much your company will suffer financially if unplanned business interruptions occur. Money that may be recovered from business interruption insurance is part of this. Calculate your losses from each part of your business to include loss from sales, loss of goodwill, aging and loss of value of inventory, etc. Now, here is the critical part: your potential loss will be a major factor in deciding how much you should spend on disaster prevention.
Next week we will continue this discussion by looking into the effect “time” will have on your disaster prevention decisions. In the meantime, we would love to start a conversation with you about disaster prevention and disaster recovery. If this is a concern of yours, and it is truly something every business executive should be thinking about, give us a call at 770.629.9615. We’ve been helping businesses just like yours as one of the top IT companies in metro Atlanta since 1992.
[featured_image]Microsoft hailed Windows 8 as “a modern computing experience for businesses that helps professionals stay connected to their colleagues and clients from anywhere, anytime.” This is a realistic assessment, but in making Windows 8 more compatible and workable on mobile devices, Microsoft did away with some features Windows users loved (the Start button, for one).
With the release of Windows 8.1 in October 2013, Microsoft brought the Start button back and made other tweaks that will increase the comfort level for users of earlier versions of Windows. It rolled numerous other enhancements into the release, which qualifies as more than an update, in our opinion.
Windows 8.1 has garnered some good reviews—and it represents the future of Windows computing for desktop and mobile users. Here’s a taste of some business-related features you can expect in the release. For more details on the user experience of the operating system, visit http://windows.microsoft.com/en-us/windows-8/features#personalize=startscreen. If you want to dig more deeply into the “under the covers” features, start here: http://technet.microsoft.com/en-us/windows/dn140266.aspx.
Mobile Device Management
Enrolled devices are connected to the Windows Intune management service, which provides users with a consistent experience for access to applications and data and enables them to manage their own devices.
NFC Tap-to-pair Printing
Users can tap their Windows 8.1 devices against an NFC-enabled printer (any printer with an NFC tag attached) and print. Wi-Fi printing is just as easy. No more hunting for printers on a network.
Remote Business Data Removal
Companies now have more control over corporate content, which can be marked as corporate, encrypted and then wiped when the relationship between the corporation and the user ends.
Improved Biometrics
All versions of Windows 8.1 include end-to-end biometric capabilities that enable authenticating with a biometric identity anywhere within Windows (Windows sign-in, remote access, User Account Control, etc.).
By DynaSis
Anyone using a computer has heard the warnings about malware and viruses—and probably other, inscrutable names like "Trojan" and "spyware." What are these threats, and does each require a separate defense strategy?
The term "Malware" covers all of types of malicious software, including viruses, Trojans and spyware. If a program is harmful in nature—whether it captures information on your operations (spyware), masquerades as a helpful program but delivers a destructive payload (a Trojan) or corrupts your hard drive (usually a virus)—it is malware.
Researchers have created different names for the various types of malware because they work through different mechanisms and/or cause different problems. However, all are intended to be harmful and can potentially disrupt or destroy your business.
More important than these distinctions, for businesses and their users, is to consider that malware (and especially insidious spyware) is exploding at a nearly inconceivable rate. The AV-TEST laboratory—a recognized malware testing lab—records approximately 5 million new malicious programs every month.
To reduce their odds of becoming victims, companies—especially those that allow workers to use Android devices (where malware and spyware are rampant)—must enact a stringent defense against all malware—from spyware to viruses and everything in between. The good news is that a single, well-designed solution will protect against the great majority of malware threats, including the ones mentioned above.
DynaSis has always offered its customers protection against malware, and we are upgrading our protection package to make it even more vigilant regarding malware and spyware. Stay tuned for more information!
For years there has been a running discussion about turning off PCs at night. One camp said turning them off saved power; the other said leaving them on reduced wear and tear on hardware. Today, energy efficient workstations with robust hardware have made both of these points largely moot.
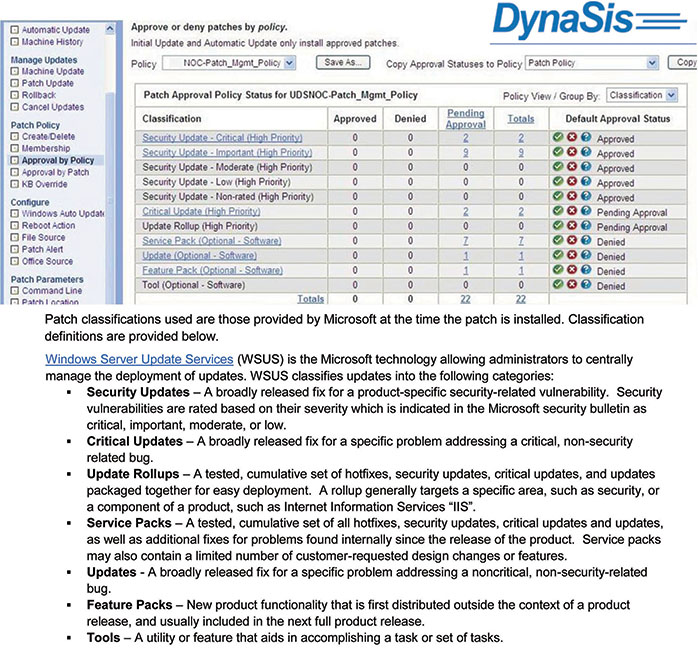
However, there is a very good reason for not turning off your workstations―at least Monday through Thursday. On each weekday night, DynaSis performs system operations, from critical system patches and virus definition updates to backups. On weekends, we usually perform operations on servers, when they are not in use. We create schedules for every company that details what we do, and when. (If you are curious what we do in the wee hours of the morning, see image below for an example.)
In fact, even setting your PC to Sleep or Hibernate mode can prevent us from performing system operations on them. Just one unavailable PC can cause the network to be out of sync and potentially increase risk for the entire office. If you and your employees feel better powering down your workstations (but not servers) over the weekend, go ahead. Most importantly, during the week, please keep workstations on and available (not in sleep or hibernate mode).
