Sales: 678.967.3854
Support: 866.252.6363
What We Do
Who We Serve
Success Stories
Latest Thinking
LATEST THINKING
About Us
By the DynaSis Team
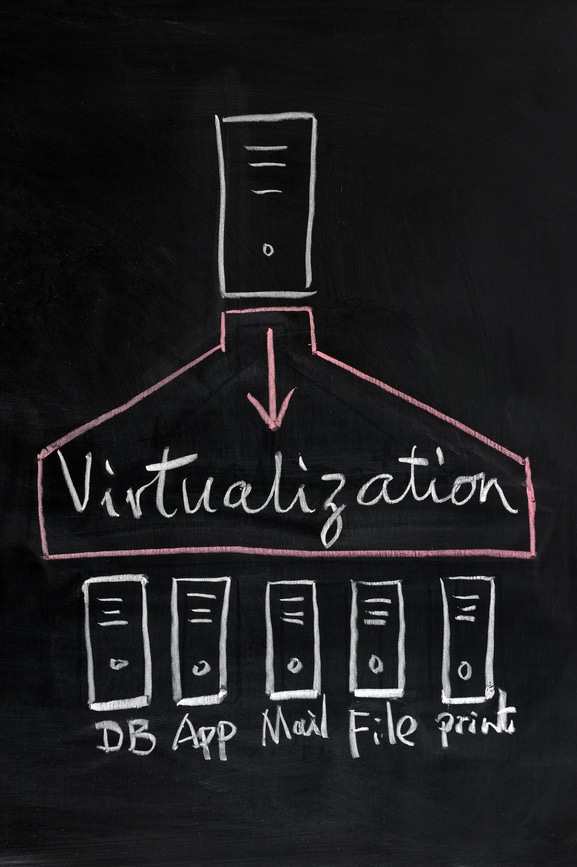
In last week’s article, we briefly mentioned virtualization in the context of our discussion on disaster recovery. For those unfamiliar with the concept, virtualization involves portioning one or more physical servers into multiple virtual machines (VMs), each of which can have its own file store, overall purpose and operating system and be isolated from the others. (Think of a VM as a sophisticated version of a partition, e.g. the C: or D: drive, on a PC.)
Virtualization greatly enhances operating efficiency and can provide a much more secure environment than a traditional server setup. Because each machine is discrete, with virtualization it can be easier to segregate and protect data of all types.
However, virtualization also increases security challenges, because there are more machines to manage―and potentially more ways for a cybercriminal to find his way in. This week, we’ll talk about a few challenges that business owners face in protecting their data in virtual environments.
Fortunately, an appropriate combination of automated monitoring and hands-on management makes it much easier to ensure visibility, management and security of VMs. DynaSis has spent nearly three decades perfecting its approach to managing and securing IT systems at all levels, from mobile devices to servers, including virtualized environments.
