Sales: 678.967.3854
Support: 866.252.6363
What We Do
Who We Serve
Success Stories
Latest Thinking
LATEST THINKING
About Us
Last week, we offered some insights into the current state of enterprise mobility and made several recommendations business leaders could implement to keep their mobile strategy updated. This week, we'll offer a list of "mobility "must haves"—features that any mobility platform should offer to ensure optimal worker productivity and security.
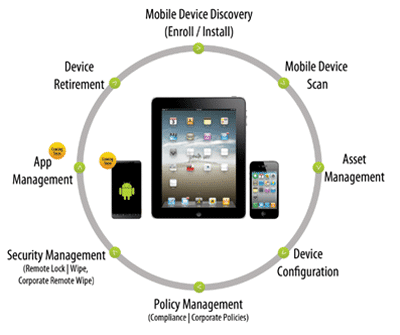
As it becomes increasingly ubiquitous and integrated into our lives, mobility brings greater complexity and risk for the organization. It also blurs the lines been roles and responsibilities of both employees and the company itself (or more accurately, the IT team). A well-designed, expertly implemented and managed mobile device solution is critical to realizing full value from mobility while protecting the company from unnecessary exposure. Following are the functions we believe to be absolute requirements for any platform.
Not a requisite for all firms, but an important addition for those that want to let users access third-party applications, is support for marketplaces such as the Apple App Store and Google Play.
If your mobile device management platform doesn't offer all of these features, or if you haven't yet deployed a solution yet, we urge you to do so, quickly. A recent mobile device security study (May 2015) found that 52 percent of mobile users conduct personal business on employer-owned devices and 21 percent have modified the default settings on their company devices. Among Millennials—which will soon compose the majority of the workforce—the numbers are even higher. Sixty-four percent use company devices for personal reasons. Even more disturbing, 25 percent of Millennials believe their device behavior compromises the security of the organization (compared with five percent for Baby Boomers).
About DynaSis
DynaSis is an Atlanta IT services and cloud computing provider for small and midsized businesses. All of our solutions focus on helping companies achieve the three fundamental IT necessities of the modern business—availability, security and mobility. We specialize in on-demand and on-premise managed IT services, managed cloud infrastructure, desktops and backups, and professional hardware and equipment installation. For more information about DynaSis’ IT support and services, visit www.dynasis.com.
