Sales: 678.967.3854
Support: 866.252.6363
What We Do
Who We Serve
Success Stories
Latest Thinking
LATEST THINKING
About Us
By the DynaSis Team
In last week’s blog, we introduced you to Shellshock, the software bug that has the entire technology world reeling due to its potential implications. Many firms, especially those with web servers, may have affected (but not necessarily infected) machines on their network and not even know it. Those with UNIX/Linux and Apple OS machines are at the highest risk level, but any network that connects to the Internet could be compromised by it.
As promised in last week’s article, this week we’ll talk a bit about network assessments and software audits. A network assessment is a process by which an in-house technical expert or a third-party provider evaluates all the devices running on a corporate network, including servers, desktops, laptops, tablets, smartphones and all other connected devices. It’s an important preventive measure against Shellshock.
At a minimum, a network assessment should be able to scan and see all the network hardware and determine whether it is protected by security software and/or devices. It should also be able to determine if the network and its devices are properly configured for optimal performance. An advanced assessment will also include a software inventory (audit) of all the software running on every machine. This level of assessment is needed to give companies a total picture of their vulnerability to the Shellshock bug.
Equally important to corporate productivity, the individuals or company performing any network assessment should be able to conduct their exploration in the background, with no impact on network resources. If software-based “discovery agents” are used, they should transmit no sensitive data out of the network. They should also be virtually undetectable by system users and should leave behind no traces of their process.
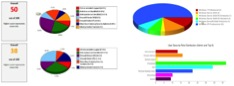
Once complete, the results should be outlined in easy-to-read reports about the network, its security weaknesses and its performance issues, as well as in an overall “score” that gives management a solid, at-a-glance idea of how their network performs. The assessment package should also include suggestions for urgent, recommended and optional improvements, with details about the issues these changes will resolve and/or benefits they will provide.
At DynaSis, we perform network assessments using a custom-built, secure solution that meets all these criteria. However, we have worked with many organizations who ordered network assessments that did not meet some―or any―of these standards.
As a comparison for your own evaluation, here’s a list of what our network assessment findings include:
Even if your network assessment and software audit reveal that Bash isn’t in use on any of your machines, it will undoubtedly root out performance and/or security problems you didn’t realize were there. After all, nine out of 10 corporate networks have network issues that are hampering worker or company productivity.
To learn more about network assessments or to ask us questions about the current threat landscape, please fill out our inquiry form or give us a call at (770) 569-4600.
